A hot potato: A ransomware attack has hit hundreds of businesses across the United States, in a supply chain attack that targets Kaseya’s VSA system management platform (used for remote monitoring and IT management). While Kaseya says less than 40 of over 36,000 customers have been reached, targeting large managed service providers has resulted in large numbers of customers further downstream.
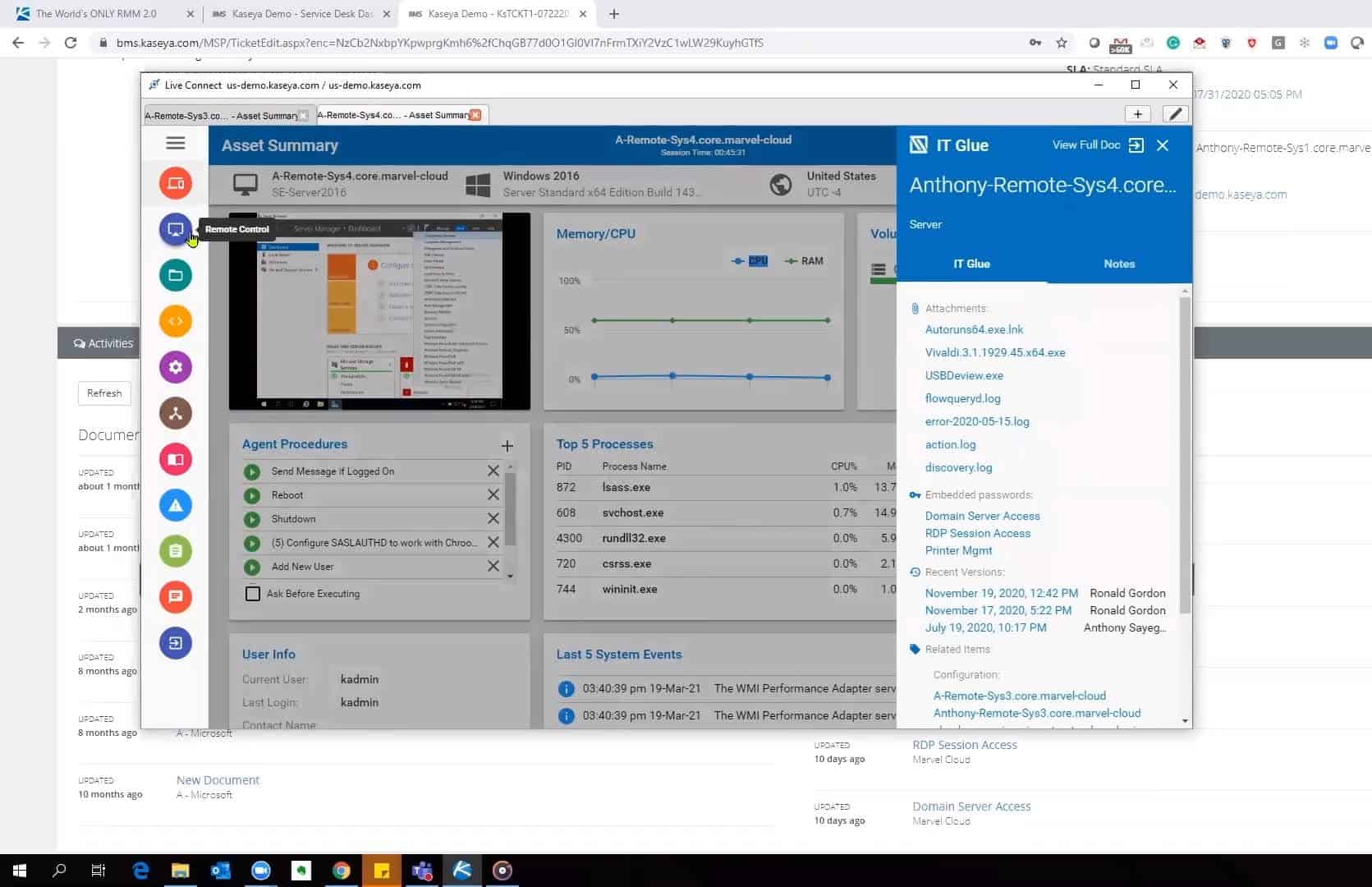
Kaseya says they were notified of a security incident around noon on Friday, as a result they put their cloud services into maintenance mode and issued a security advisory advising all customers with a local VSA server to shut it down until. ‘again, like’ One of the first things the attacker does is cut off administrative access to the VSA. Kaseya also informed the FBI and the CISA and launched her own internal investigation.
The company’s second update stated that the VSA cloud shutdown was only done as a precaution and that customers using their SaaS servers “were never at risk.” However, Kaseya also said that these services will remain suspended until the company determines it is safe to resume operations, and at the time of writing the VSA cloud suspension has been extended until 9 a.m. ET.

The REvil ransomware gang appears to have its payload delivered via a standard automatic software update. It then uses PowerShell to decode and extract its content while simultaneously removing many Windows Defender mechanisms, such as real-time monitoring, cloud search, and controlled folder access (Microsoft’s built-in anti-ransomware feature). This payload also includes an older (but legitimate) version of Windows Defender, which is used as a trusted executable in order to launch a DLL with the encryptor.
It is not yet clear whether REvil steals data from victims before activating their ransomware and encryption, but the group is known to have done so in previous attacks.
The scale of the attack is still ongoing; Supply chain attacks like these that compromise weak links further upstream (instead of directly hitting targets) have the potential to wreak havoc on a large scale if those weak links are used extensively – like the VSA of Kaseya, in this case. In addition, his arrival on the weekend of July 4 appears to have been timed to minimize the availability of staff to deal with the threat and slow down the response to it.

BleepingComputer initially said eight MSPs were affected and cybersecurity firm Huntress Labs knew of 200 companies compromised by the three MSPs it worked with. However, further updates from Huntress’s John Hammond show that the number of affected MSPs and downstream customers is much higher than these early reports and continues to grow.
The demands have varied enormously. Intended to be paid in Monero cryptocurrency, most ransoms appear to start at $44,999, but they can go up to $ 5 million. Likewise, the payment due date – after which the ransom is doubled – also seems to vary from victim to victim.
Of course, both figures are likely to depend on the size and scale of the intended target. REvil, which U.S. officials say has ties to Russia, secured $ 11 million from JBS meat processors last month and demanded $ 50 million from Acer in March.
